I recommend disabling this plugin if you are using it and as an alternative, I've provided a quick-fix solution that will generate meta tags automatically based on the content of an entry. That solution can be found here.
This CVE is registered with cve.mitre.org, the CVE page is located here (may not be available yet).
The vulnerability is exposed if the SEO Metatag Info Plugin is installed and enabled. This plugin attempts to generate meta tag info for all requests coming into FlatPress. This includes requests for 'categories'. FlatPress provides functionality for defining categories, unfortunately the SEO Metatag Info Plugin does not restrict it's functionality to the list of these pre-defined categories.
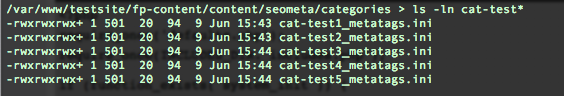
When a request is issued for a category that's not been previously defined, the SEO Metatag Info Plugin will write an .ini file that describes that category's metadata. In the case of an undefined category this always writes a 94 byte file with default contents to the fp-content/content/seometa/categories directory. The name of the requested category is included in the file.
For example, requesting the 'test1', 'test2', 'test3', 'test4', 'test5' categories results in the following files being written to disk:
These requests are made by generating URLs in the following format:
Test URLs
http://<server>/?cat=<category_name>
Here category_name can be substituted for any string value and the plugin will take that string and will write a file in the following format:
Generated files
fp-content/content/seometa/categories/cat-<category_name>_metatags.ini
Although each file is quite small, repetitive requests to a vulnerable system can generate an indefinite number of files. If the web server limits quotas using inodes, this can quickly consume all of the available inodes.
-i
